5 Essential Things to Know About HashiCorp Vault's New AI Agent Security Capabilities
As organizations increasingly deploy AI agents for autonomous decision-making, traditional identity and access management (IAM) models fall short. These agents operate non-deterministically, requiring authorization that is dynamic, ephemeral, and tightly scoped to each task. HashiCorp Vault now introduces native support for AI agents with a dedicated set of security controls. This listicle explores the key features—from a new agent registry to per-request authorization—that help organizations secure agentic workflows while maintaining least privilege and auditability.
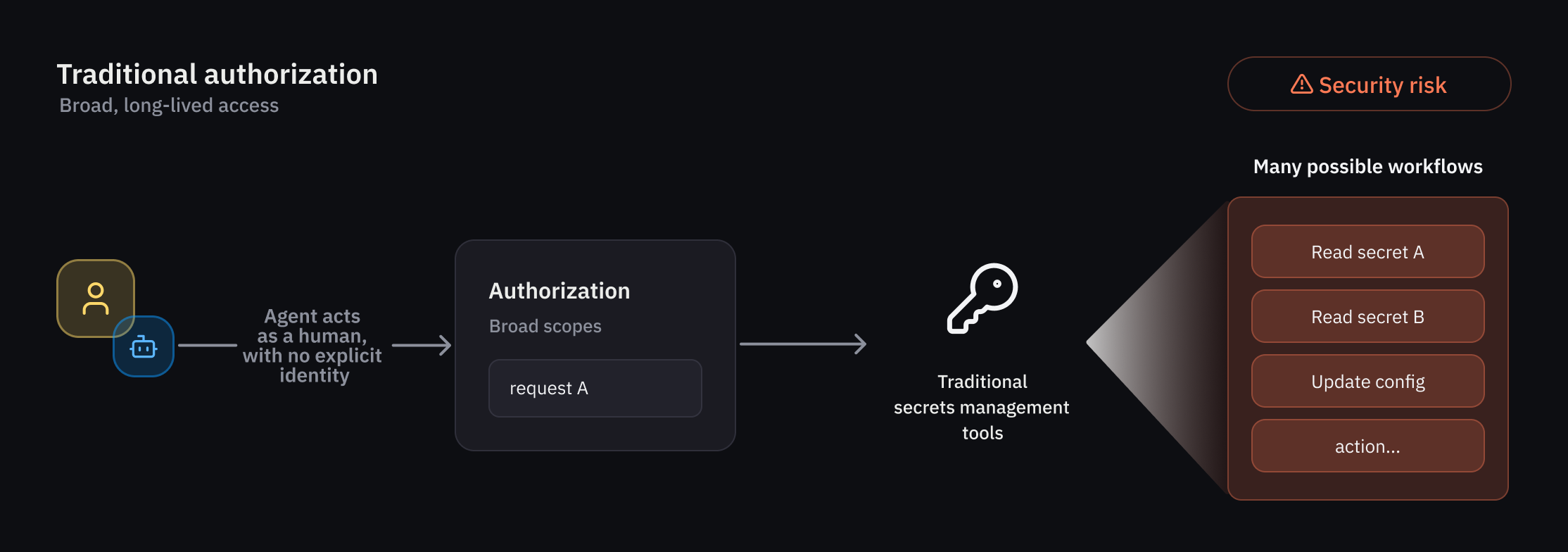
1. Why AI Agents Demand a New Authorization Model
Traditional IAM was built for deterministic users and predictable workflows. AI agents, however, introduce autonomous, non-deterministic actors that require a fundamentally different approach. These agents often act on behalf of humans, using on-behalf-of (OBO) delegation patterns, and their behavior can vary with context. Authorization must therefore be temporary, scoped to a specific transaction, and evaluated at runtime. Vault addresses this by combining identity, delegation, runtime policy evaluation, and ephemeral authorization—moving beyond simple access controls to a model that adapts to each request's unique context. This shift is critical because agents may request credentials for target systems based on changing conditions, and static permissions would either be too permissive or too restrictive. By treating each agent action as a discrete event, Vault ensures that access is granted only for the duration and scope necessary, reducing the risk of credential abuse or lateral movement.
2. The Agent Registry: A Centralized Hub for Agent Identities
To manage agent activity separately from human and traditional non-human identities (NHIs), Vault introduces a dedicated agent registry. This registry allows developers to register and oversee every AI agent in an organization, providing a distinct identity primitive. The agent registry is especially valuable in delegation flows, where an agent uses OBO patterns from a human user. By explicitly tracking this delegation—including consent and scope—the registry forms the foundation for a comprehensive framework covering registration, authorization, credential management, and observability. Administrators can view which agents are active, what human they act for, and what permissions have been delegated. This separation of concerns ensures that agent-specific oversight is not lost in a sea of human and machine identities, enabling targeted auditing and policy enforcement. The registry also simplifies onboarding new agents and revoking access when an agent is decommissioned or compromised.
3. Granular Identity-Based Policies for Runtime Control
Least privilege access is paramount, especially for non-deterministic agents. Vault enforces this through rich, policy-based runtime controls that allow administrators to strictly govern agent activity. Because agent behavior can vary unpredictably, Vault applies deterministic guardrails alongside per-request access control. Policies can be defined based on agent identity, the human delegator, the context of the request, and the target resource. For instance, an agent may be allowed to read secrets only from a specific secrets engine and only between certain hours, or it may be required to obtain fresh consent from its human user every few minutes. These granular policies ensure that even if an agent takes an unexpected action, it stays within predefined boundaries. Additionally, when agents operate in delegation mode—carrying the authority of a human user—Vault evaluates trust across multiple dimensions, combining the agent's identity, the delegating user's permissions, and the specific task. This multi-dimensional evaluation prevents privilege escalation and ensures that agents cannot perform actions their human counterparts could not.
4. Per-Request Ephemeral Authorization for Temporary Access
One of the most powerful features for AI agents is ephemeral authorization, which grants temporary access rights that expire after a specific task or timeframe. This reduces the risk of credential leakage or misuse, as there is no long-lived token for an attacker to steal. For each request, the agent must obtain a short-lived credential—such as a dynamically generated token or one-time password—that is scoped exactly to the required action. Vault integrates this per-request authorization with the agent registry and identity-based policies, so every access request is validated against the agent's identity, delegation context, and policy constraints. This approach aligns with the transient nature of agent interactions: an agent may need to read a database, then call an API, then update a file—each step requiring separate credentials. By making authorization a first-class part of each request, Vault ensures that agents operate under the principle of least privilege and that all actions are fully auditable. Administrators can review logs to see exactly which agent performed which action, with which credential, and for how long.
5. Early Access and Future Public Beta Availability
These capabilities—agent registry, identity-based policies, and ephemeral authorization—are currently being evaluated by select customers through an early access program. Feedback from these early adopters will help refine the feature set before a broader public beta, which HashiCorp plans to release later this summer. The early access program covers a range of use cases, from simple secret retrieval to complex multi-step workflows where agents act as orchestrators. Organizations interested in securing their AI agents are encouraged to apply, as the program provides hands-on experience with the new primitives. Looking ahead, the public beta will expand support to more environments and workflow patterns, including integrations with popular agent frameworks and cloud providers. HashiCorp is also exploring additional capabilities such as dynamic consent management and AI-specific audit dashboards. These developments underscore the company's commitment to leading the way in securing autonomous systems without sacrificing operational flexibility.
In summary, HashiCorp Vault's new AI agent security features address the unique challenges of non-deterministic, delegated, and ephemeral access patterns. By introducing a dedicated agent registry, granular identity-based policies, and per-request authorization, Vault empowers organizations to adopt AI agents confidently while maintaining strict security controls. As the technology moves from early access to public beta, it promises to become an essential tool for any enterprise leveraging autonomous agents.
Related Discussions